A multi‑environment workstation can securely host one or several Restricted Distribution environments locally, without resorting to heavy segmentation models such as physical isolation. In its guideline, ANSSI formalizes a model many public and private organizations have been waiting for: strong isolation with no friction for the end-user.
What is a multi‑environment workstation?
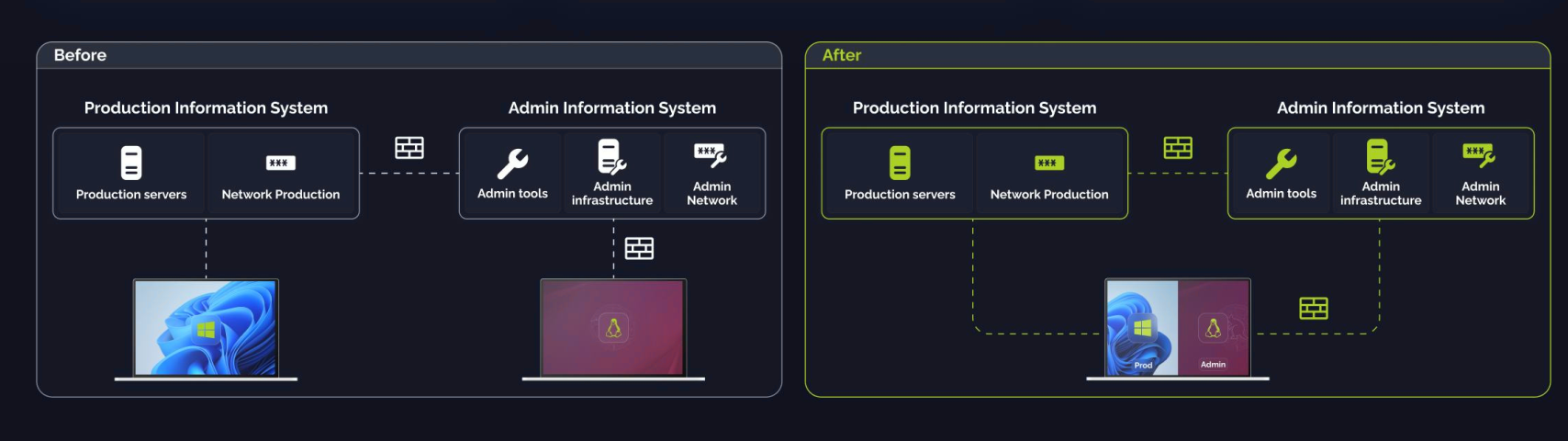
A multi‑environment workstation is a single‑user endpoint designed to host and isolate two or more IT systems (or environments) on the same physical machine.
It enables a user to operate multiple distinct environments (e.g., an office productivity environment and an administration environment) on one physical workstation while maintaining strong isolation.
What are the requirements for a multi‑environment workstation?
A multi‑environment workstation relies on several core security principles:
- Logical isolation
- Dedicated VM for each usage domain
- Strict network flow control (firewall, segmentation)
- Non-bypassable VPN bound to each environment
- Hardened security base
- Secure Boot / Measured Boot
- TPM as a hardware root of trust
- Minimal and controlled TCB (Trust Computing Base)
- Operational security
- Full-encryption and secret protection
- Segregated logging
- Strong control over inter‑domain communications (e.g., unidirectional data diode)
Why is ANSSI document about multi-environment workstations important?
ANSSI’s document is significant because it acknowledges the limitations of traditional models which often hinder mobility and create operational friction. In its guidance, ANSSI highlights several recurring issues:
- The mobility paradox: When environments have heterogeneous sensitivity levels, physical separation remains the security reference model… but it often conflicts with mobility needs, costs, and environmental footprint.
- Traditional approaches (strict VDI, dual‑workstation setups, secure rooms) increasingly conflict with modern usage requirements.
- Conventional security measures often introduce heavy operational friction: multiple authentications, dedicated machines, restrictive networking, limited mobility, etc.
MEWs offer a pragmatic alternative that preserves isolation without burdening the end user. ANSSI therefore proposes a robust framework for designing secure multi‑environment workstations fully aligned with what we have been building at KERYS Software since 2024.
What are the advantages of a multi‑environment workstation?
The multi‑environment workstation adopts a realistic approach to isolation that reduces the attack surface without dramatically increasing cost or operational complexity.
How to implement a multi‑environment workstation?
To deploy multi‑environment workstations, organizations should rely on solutions that meet ANSSI’s technical requirements.
The security base must match the most sensitive domain, maintain strict isolation even when environments share a sensitivity level, and allow inter‑domain communication only through authorized, controlled mechanisms. KERYS Software supports this approach with its Type‑1 hypervisor, providing complete isolation without degrading user experience.
What is the difference between classified and unclassified information?
In the French law, the distinction between classified and unclassified relates to the confidentiality level of information or media. Classified information is material whose disclosure or access could harm national defense or security.
Two levels of classified information exist: Secret and Top Secret.
“The Secret level protects information and media whose disclosure or access could harm national defense and security. The Top Secret level protects those whose disclosure or access would have exceptionally grave consequences.” (French Interministerial General Instruction No. 1300)
French mention “Diffusion Restreinte” (Restricted Distribution) is not a classification level but a sensitivity designation.
What is the difference between multi‑level and multi‑environment workstations?
Both multi‑level and multi‑environment workstations allow multiple environments to run on the same physical device. The difference lies in the nature of these environments.
A multi‑level workstation hosts environments with different classification levels (e.g., Classified / Unclassified). A multi‑environment workstation hosts distinct technical environments, all unclassified (e.g., NP/NP, NP/DR, DR/DR).
As a result, a multi‑environment workstation can host more than two segregated environments, whereas a multi‑level workstation typically hosts only two.
Can VDI be used to build a multi‑environment workstation?
Yes, but using VDI to build a MEW might result in degraded performance.
In practical terms, in the lack of physical separation of workstation, the preferred option is to use a multi‑environment workstation that enables local data hosting. However, if local hosting of the VMs on a single physical workstation is not feasible, a lower‑security fallback may be to rely on a remote access solution, such as VDI.